How to generate strong passwords using music theory

I am passionate about music and, in one night, I came up with an idea about how to generate strong passwords that are relatively easy to remember using music theory. In this article I am going to explain the foundations of this method, but firstly, a little background about passwords.
Why do we need strong passwords?
Usually, we are using passwords to restrict the access on different platforms that offer a large variety of services: social media, medical, bank, etc. In the simplest form, a password is a simple string of characters. Together with the username or another type of ID, the password certifies our identity. With the new methods of authentication, like 2FA and captcha, we can suppose that the password's strength is not a crucial factor in security of our accounts. However, the statistics and recent security research reveal the opposite: compromised passwords are responsible for 81% of hacking-related breaches (NIST)(COVEWARE). A relevant example is the Sunburst attack in which the attackers used a weak password, solarwinds123, posted on Github to gain access on a FTP server.
What strong password does it mean?
NIST had published an article named Digital Identity Guidelines - Authentication and Lifecycle Management (NIST Special Publication 800-63B) which contain some guidelines about how to create a strong password. The main factors the contribute to password's strength are:
- length - primary factor that characterize the strength; the password should be as long as the user want but must be at least 8 characters in length;
- complexity - a password must contain characters from 4 distinctive sets:
- digits
- uppercase letters
- lower case letters
- special characters
Here are some examples of strong passwords:
- xsiDYvr1OU0bhI
- 2CgNs9l3DYBYOk
- 3hBTWc9EAJIs8K
Also, there is another important aspect regarding password's strength. It must not contain any word from any language because there are brute force attacks that are using dictionaries to generate passwords.
Moreover, a strong password must not contain personal information as well. Some examples are:
- date of birth
- pet name
- maiden name etc.
All of these data can be obtained from social media channels or information leakage from various platforms. See linkedin and facebook cases.
Moreover, for a long term security it is recommended to change your password once every 60-90 days.
How to generate and remember strong passwords
zdBTV29hm|)r>lU
This is a very strong password generated using bitwarden. According to kaspersky password checker, it would take 3261 centuries to broke this password using nowadays computing power. How do we generate such a password and how to remember it?
Password generation
It is recommended to generate and manage your passwords using a password manager. There are many options out there and they take care of a lot of aspects of password security that are not covered in this article. So, feel free to choose from 1Password, bitwarden, keeper and many more.
But regarding "manual" password generation, there is a study that shows that the humans are not very good to generate random number sequences. I am going to overcome this issue using a funny method to generate strong passwords later in this article, but I don't recommend to be used in daily life. The password managers remain the standard.
Do you remember me?
Now the hard part comes in play. How do you remember a strong password like zdBTV29hm|)r>lU ?
If you are like Kim Peek it is no a big deal. Or you can use card memorization techniques to remember each character of the password. Or ...
Ok. Let me propose another password:
DMaj7|Fsus2!G#9
According to kaspersky, this password requires 3261 centuries to be broken by a brute force attack. Compared to the previously tool-generated password, it has the same strength and the same length. However, it is much easier to remember, at least in my opinion.
If you don't get my point let's transcribe the password in another format.
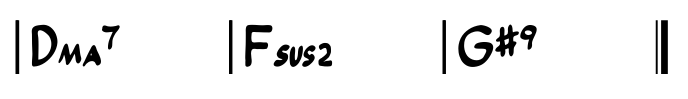
If you play the guitar or if you are familiar with music theory everything should be clear now. If not, let me explain.
The above figure is a music score with 3 chords. In the western musical notation the notes are represented by letters from A to G. The first letter in a chord is the root and the following symbols are different intervals inside the chord. The chords are separated by bars. I leave here a link with more details about music theory.
If we try to describe the above password using the musical language it will be:
D Major Seventh | F suspended 2 | G sharp 9
Now, how to generate a password using music theory?
We can use a simple pattern like <Chord><Bar><Chord><Bar> etc, like in the above figure. Also, a <Chord> can be decomposed in <Root><Flat/Sharp> and <Intervals>. Some examples are:
Gm7(9), Am7(b13 9), DmMaj7, B7#5, Csus2/G
You can use music theory from the provided link or the chords of your favorite songs. There are a plenty of sites that provide scores for free like Ultimate Guitar and Guitare Tab.
However, you have to use complex intervals in each chord to obtain a strong password. If you try to play on the guitar
DMaj7|Fsus2|G#9
you will end up in tears 😂. So, I think that most songs are not suitable for strong password generation. Maybe if you love jazz you will find something useful there.
Music theory-based alphabet for password generation
I leave a short list with the available symbols that can be used to generate passwords.
- Chord root: A, B, C, D, E, F, G
- Flat/Shard: b, #
- Intervals: 1 → 13, m7, Maj7, sus2, sus4, dim7, etc.
- Bar: |, !, l (lower case L), I (upper case i)
Here you can listen to DMaj7|Fsus2|G#9 (Ab9 = G#9). Enjoy!
Updates regarding security concerns about this password generation method
As I mentioned earlier, the method that I presented in this article is just a funny thing that I discovered. I don’t encourage you to use it and if you want to give it a try you are at your own risk. To secure your account, you should use password generators and 2FA, where it is possible.
We’ve seen that a password like DMaj7|Fsus2!G#9 would take 3261 centuries to be broken by a brute force attack. However, this estimation was valid before this article was published. By the moment you read this, there is a chance that someone integrated my method in a password cracking tool like John the Ripper. If this is the case, the password can be broken in much less time, maybe minutes.
Further reading
If you are curious about how many chords are there in music, I suggest reading this article. Also, if you want to understand the chords’ structure better, here you have a great resource. It would be nice if someone would compute the entropy for this method and the minimum number of chords needed to obtain a really strong password, but I think that this task is quite complex as it stands out from the suggested articles.
Also, I leave here another interesting method that creates strong and easy to remember passwords. Its name is Diceware, and it’s well documented. Have fun!
Regarding privacy, you have here a good complementary resource.
If you want to boost your security, you can check this password generator, which also provides tips on password management and best practices for protecting personal information online.
📩 Please feel free to share this article with colleagues and friends who will find it valuable.